AAROS (Aegis Active Response Operating System)
Main Article Content
Abstract
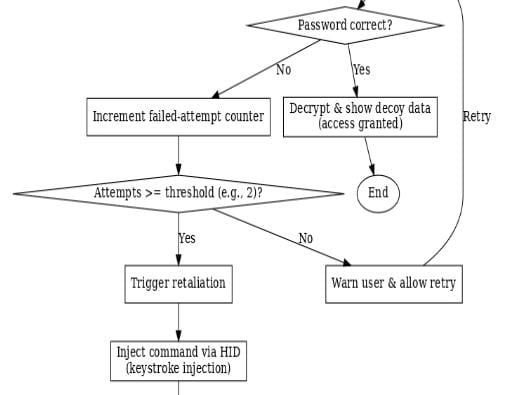
An AAROS (Aegis Active Response Operating System), a novel retaliatory red teaming tool designed to address the limitations of passive defensive security measures. The persistent threat of unauthorized access to sensitive data often leaves organizations with reactive, post-incident forensic analysis rather than proactive countermeasures. AAROS proposes a new paradigm by employing a low-cost Raspberry Pi, configured as a Human Interface Device (HID), to serve as a decoy system. The device hosts a sensitive data folder secured with strong cryptography, requiring correct credentials for access. The core functionality of AAROS is its retaliatory mechanism: upon the detection of failed credential attempts or unauthorized access, the HID automatically executes a pre-configured C2 (Command and Control) malware payload on the attacker's system. This action not only deters malicious actors but also establishes a connection to the attacker's machine, allowing for immediate control and intelligence gathering. Our methodology details the system architecture, hardware and software components, and the cryptographic and payload deployment mechanisms. The results demonstrate the viability of this approach in controlled test environments, confirming the device's ability to reliably detect unauthorized access and successfully deploy a C2 payload to gain control over the attacker's machine. AAROS provides a unique and effective strategy for red teaming, offering a proactive, real-time response that moves beyond traditional perimeter defenses and static detection systems.
Downloads
Article Details

This work is licensed under a Creative Commons Attribution-NoDerivatives 4.0 International License.